After it’s stellar IPO, Zoom seemed to be on the path to becoming one of the greatest SaaS success stories. When the COVID-19 imposed lockdowns started spreading across Western geographies, where Zoom already had a solid enterprise user base such as the US & Europe, the company’s daily active users jumped spectacularly from 10 million to 200 million! But unfortunately, the excitement was to be cut short when reports about Zoom’s security flaws such as ‘Zoombombing’ came to light. The company’s Co-Founder & CEO, Eric Yuan, was quick to issue an apology:
‘‘For the past several weeks, supporting this influx of users has been a tremendous undertaking and our sole focus. We have strived to provide you with uninterrupted service and the same user-friendly experience that has made Zoom the video-conferencing platform of choice for enterprises around the world, while also ensuring platform safety, privacy, and security. However, we recognize that we have fallen short of the community’s – and our own – privacy and security expectations. For that, I am deeply sorry, and I want to share what we are doing about it.’’
Outsourcing Security Due Diligence
Our parent company Zaiku Group recently surveyed Zoom users under the condition of anonymity including users from some of the enterprise customers listed on Zoom’s website. Staggeringly, we found out that 70% of the users did not conduct due diligence, nor are they aware that their company did! Why would that be the case? Of those who did not conduct due diligence, 41% said they did not have the time nor the skills to do so. Whereas, 59% said they trusted using Zoom because other well-respected & capitalized brands were already the service and so assumed these brands did their due diligence i.e by proxy they outsourced due diligence to these ‘well-respected & capitalized brands’!
The Citizen Lab Report
Security researchers from the Canadian organization called The Citizen Lab wrote a very comprehensive report on their security analysis of Zoom that was conducted recently. For the reader in a rush, we extracted a good chunk of key parts of the report below:
Any Feature You Like, As Long As It’s Speed
In the past few years, a number of security issues regarding Zoom have come to light. These issues have included unintentional bugs, such as vulnerabilities in Zoom’s screen sharing feature, and privacy concerns, such as Zoom sharing data with Facebook. However, perhaps the most prominent security issues with Zoom surround deliberate features designed to reduce friction in meetings, which also, by design, reduce privacy or security. This includes Zoom installing a hidden web-server on Mac computers to circumvent a Safari popup that users had to click through before they joined a Zoom meeting, a Zoom feature that removes a password prompt during the installation process (and instead displays a misleading password prompt later), a Zoom feature intended to allow Zoom users at the same company (or ISP) to easily find each other, and Zoom’s easy 9 or 10 digit code which is sufficient to join a meeting created with default settings, leading to the well-reported phenomenon of “Zoom Bombing.”
Encryption Questions Come to Light
Zoom’s documentation has a number of unclear claims about encryption that the platform offers. Some Zoom documentation (as well as the Zoom app itself) claims that Zoom offers a feature for “end-to-end (E2E) encrypted meetings.
Typically, the computer security community understands the term “end-to-end encrypted” to mean that only the parties to the communication can access it (and not any middlemen that relay the communication). Other Zoom documentation says that Zoom’s meeting software for Windows, MacOS, and Linux “by default” uses the industry-standard TLS 1.2 scheme for transport encryption, though a September 2014 blog post implies that this software does not use TLS.
In response to this confusion, Zoom released a blog post in April 2020 describing their encryption scheme. The blog post clarifies that Zoom does not currently implement “end-to-end” encryption as most people understand the term; Zoom used the term “end-to-end” to describe a situation where all conference participants (except those dialing in via the public switched telephone network) are required to use transport encryption between their devices and Zoom servers. Zoom’s definition of “end-to-end” does not seem to be a standard one, even in the realm of enterprise videoconferencing solutions. Because Zoom does not implement true end-to-end encryption, they have the theoretical ability to decrypt and monitor Zoom calls. Nevertheless, Zoom mentions that they have not built any mechanism to intercept their customers meetings: “Zoom has never built a mechanism to decrypt live meetings for lawful intercept purposes, nor do we have means to insert our employees or others into meetings without being reflected in the participant list.”
Zoom’s April 2020 blog post does not, however, provide details about exactly how their encryption works, or clarify whether they use TLS or AES-256. Because of the potentially misleading and conflicting claims regarding Zoom’s encryption, and the proliferation of Zoom’s technology in the business, government, civil society, and healthcare sectors where confidentiality may be desired, we decided to examine exactly how Zoom meetings are encrypted.
Interactions that were previously conducted in the real world are now mediated by popular digital platforms. Until a few weeks ago, it would have been uncommon for high stakes business negotiations, high level diplomacy, political strategy conferences, and cabinet meetings to be conducted over platforms whose security properties are unknown. Eavesdropping on these encounters would have been out of reach to all but the most sophisticated digital adversaries.
Now, some of the most sensitive conversations in the world are taking place on devices and platforms vulnerable to basic forms of eavesdropping and attack techniques. This “new normal” is a potential goldmine for cyber spies. Given the business value of meetings currently being conducted on Zoom, it is reasonable to expect that the platform is being closely scrutinized by groups engaged in industrial and political espionage, and cybercrime.
COVID-19: A New Gold Rush for Cyber Spies
Social distancing and work-from-home policies have shifted government, economic, and personal activity online. In the rush to reconnect, users are rapidly adopting new apps and communications platforms. Some popular video chat and collaboration tools have added millions of users, almost overnight. In many cases, consumer choice appears to be driven by the need for usability, speed, and stability, rather than careful assessment of privacy policies and security protocols.
At the same time, the newly remote workforce is heavily reliant on personal equipment and online accounts for work business. The shift away from work networks and accounts denies cyber defenders the ability to enforce security standards, while blocking their visibility into potential compromises.
Figure 4: UK PM Boris Johnson conducting a cabinet meeting over Zoom (Source).
Interactions that were previously conducted in the real world are now mediated by popular digital platforms. Until a few weeks ago, it would have been uncommon for high stakes business negotiations, high level diplomacy, political strategy conferences, and cabinet meetings to be conducted over platforms whose security properties are unknown. Eavesdropping on these encounters would have been out of reach to all but the most sophisticated digital adversaries.
Now, some of the most sensitive conversations in the world are taking place on devices and platforms vulnerable to basic forms of eavesdropping and attack techniques. This “new normal” is a potential goldmine for cyber spies. Given the business value of meetings currently being conducted on Zoom, it is reasonable to expect that the platform is being closely scrutinized by groups engaged in industrial and political espionage, and cybercrime.
Zoom as an Intelligence Target
Zoom’s success has led it to attract conversations that are of high priority interest to multiple governments. We suspect that this makes Zoom a high priority target for signals intelligence (SIGINT) gathering and targeted intrusion operations.
Most governments conduct electronic espionage operations. Their targets include other governments, businesses, and individuals. Some, including the Chinese government, are known to conduct extensive industrial espionage. In addition, a growing number of governments have sought out mobile phone hacking technology and abused it to target the personal phones of journalists, lawyers, judges, and others who seek to hold them to account.
In addition, as digital rights advocacy group Access Now has pointed out in an open letter calling for a transparency report, Zoom has not publicly disclosed information such as statistics of requests for data by governments, and what Zoom has done in response to these requests. Zoom’s policies concerning notifications to users over breaches or the handing-over of data to governments are also unknown, however the company has just promised at the time of writing to release such a report within 90 days of April 2nd.
Custom Crypto, Chinese Servers, Security Issues
Rather than using a standard protocol for sending voice and video, Zoom appears to implement their own transport protocol. The Zoom transport protocol appears to be a bespoke extension of the existing RTP standard.
The Zoom transport protocol adds Zoom’s own encryption scheme to RTP in an unusual way. By default, all participants’ audio and video in a Zoom meeting appears to be encrypted and decrypted with a single AES-128 key shared amongst the participants. The AES key appears to be generated and distributed to the meeting’s participants by Zoom servers. Zoom’s encryption and decryption use AES in ECB mode, which is well-understood to be a bad idea, because this mode of encryption preserves patterns in the input. Industry standard protocols for encryption of streaming media (e.g., the SRTP standard) recommend the use of AES in Segmented Integer Counter Mode or f8-mode, which do not have the same weakness as ECB mode. Figure 5 is a classic illustration of the perils of ECB mode: the outline of a penguin is still visible in an image encrypted with ECB mode.1
During a test of a Zoom meeting with two users, one in the United States and one in Canada, we found that the AES-128 key for conference encryption and decryption was sent to one of the participants over TLS from a Zoom server apparently located in Beijing, 52.81.151.250. A scan shows a total of five servers in China and 68 in the United States that apparently run the same Zoom server software as the Beijing server. We suspect that keys may be distributed through these servers. A company primarily catering to North American clients that sometimes distributes encryption keys through servers in China is potentially concerning, given that Zoom may be legally obligated to disclose these keys to authorities in China.
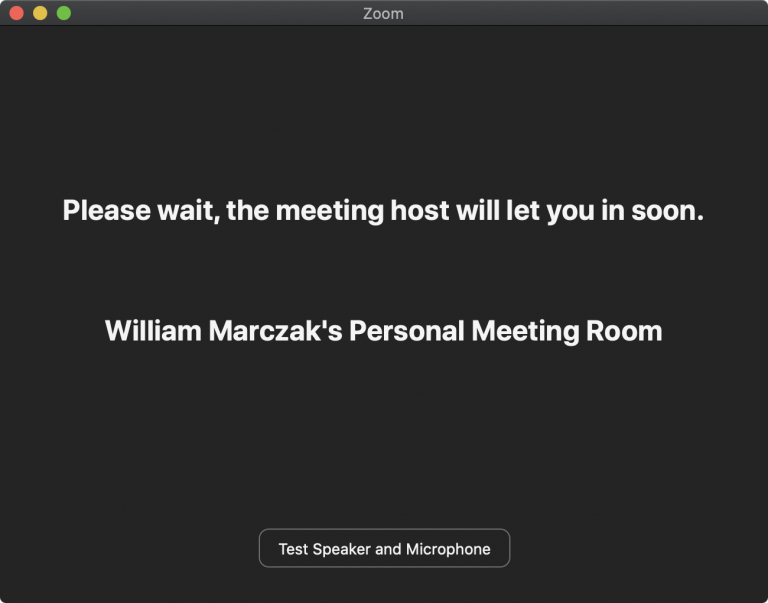
During our analysis, we also identified a security issue with Zoom’s Waiting Room feature. Assessing that the issue presented a risk to users, we have initiated a responsible vulnerability disclosure process with Zoom. We are not currently providing public information about the issue to prevent it from being abused. We intend to publish details of the vulnerability once Zoom has had a chance to address the issue. In the meantime, Section 5 provides recommendations on how users can mitigate the issue.
How we Investigated
We began by observing Internet traffic associated with Zoom meetings using the Zoom clients on Windows, MacOS, and Linux. We used Wireshark to record our Internet traffic while we joined and participated in Zoom meetings. The vast majority of the Internet traffic during our Zoom meetings was exchanged between our computer and servers owned by Zoom on UDP port 8801. A further examination of the UDP traffic revealed that Zoom had apparently designed their own transport protocol, which wraps the well-known RTP protocol for transferring audio and video. [More reference on the methods used by the researchers can be found here]
Conclusion: Not Suited for Secrets
Zoom’s product is user-friendly and has rapidly grown its user base during the COVID-19 pandemic by “just working.” Zoom’s fast growing user base, combined with marketing language around encryption and security, have attracted many sensitive conversations. This sudden popularity likely puts the product in the crosshairs of government intelligence agencies and cybercriminals.
Questionable Crypto & Encryption Keys Sent to Beijing
Unfortunately for those hoping for privacy, the implementation of call security in Zoom may not match its exceptional usability. We determined that the Zoom app uses non-industry-standard cryptographic techniques with identifiable weaknesses. In addition, during multiple test calls in North America, we observed keys for encrypting and decrypting meetings transmitted to servers in Beijing, China.
An app with easily-identifiable limitations in cryptography, security issues, and offshore servers located in China which handle meeting keys presents a clear target to reasonably well-resourced nation state attackers, including the People’s Republic of China.
Our report comes amidst a number of other recent research findings and lawsuits identifying other potential security and privacy concerns with the Zoom app. In addition, advocacy groups have also pointed out that Zoom lacks a transparency report, a critical step towards addressing concerns arising when companies have access to sensitive user data. Zoom has just stated (April 2nd, 2020) that it will release such a report within 90 days.
As a result of these troubling security issues, we discourage the use of Zoom at this time for use cases that require strong privacy and confidentiality, including:
Governments worried about espionage
Businesses concerned about cybercrime and industrial espionage
Healthcare providers handling sensitive patient information
Activists, lawyers, and journalists working on sensitive topics
For those using Zoom to keep in touch with friends, hold social events, or organize courses or lectures that they might otherwise hold in a public or semi-public venue, our findings should not necessarily be concerning.
For those who have no choice but to use Zoom, including in contexts where secrets may be shared, we speculate that the browser plugin may have some marginally better security properties, as data transmission occurs over TLS. - Citiziens Lab
Now, going back to the subject of whether you should be worried. In our humble opinion, this will greatly depend on your organization’s risk tolerance given that although it is technically feasible that an insider in Zoom’s engineering workforce could, for example, collude with bad actors for say industrial espionage, the chances are very small because of the degree of complexity that would be required to accomplish such a task without other Zoom engineers noticing. Hence, to accomplish this, the entirety of Zoom’s engineering workforce would have to collude with bad actors, or at least be scared enough not to disclose the act to Zoom’s senior management in the US.
The risk for Zoom is that it will be very damaging for the company if more sizeable security flaws come to light. The company could find itself in hot water, with Mr. Trump potentially taking the unprecedented step of placing a US-born tech company in the same place as Huawei!
Disclaimer: Any opinions, newsletters, research, analyses, prices, projections or other information offered by Kähler AI is provided as general market commentary, and does not constitute investment advice. Kähler AI will not accept liability for any loss or damage, including without limitation to, any loss of profit, which may arise directly or indirectly from use of or reliance on such information. ZAIKU GROUP LTD.